Multi-tenant RLS architecture
Tenant-scoped data and row-level security policies protect account boundaries across the platform.
- Tenant-scoped tables
- Account-bound policies
- User-request boundaries
Security and governance
Squawker publishes a direct trust surface for security overview, RLS architecture, data residency options, subprocessors, privacy posture, monitoring, and SOC 2 preparation.
SOC 2 is in preparation.
Security review map
Trust content should be direct: what is ready, what is in preparation, which dependencies exist, and who to contact when security review gets specific.
Tenant-scoped data and row-level security policies protect account boundaries across the platform.
The trust page lists residency options and core subprocessors so enterprise teams can review dependencies early.
Call recording, consent, retention, and privacy details need a plain public explanation before enterprise security review.
Sentry monitoring, incident response, SOC 2 preparation, and vulnerability contact details belong on one public route.
Why buyers care
Tenant-scoped data and row-level security policies protect account boundaries across the platform.
The trust page lists residency options and core subprocessors so enterprise teams can review dependencies early.
Call recording, consent, retention, and privacy details need a plain public explanation before enterprise security review.
Sentry monitoring, incident response, SOC 2 preparation, and vulnerability contact details belong on one public route.
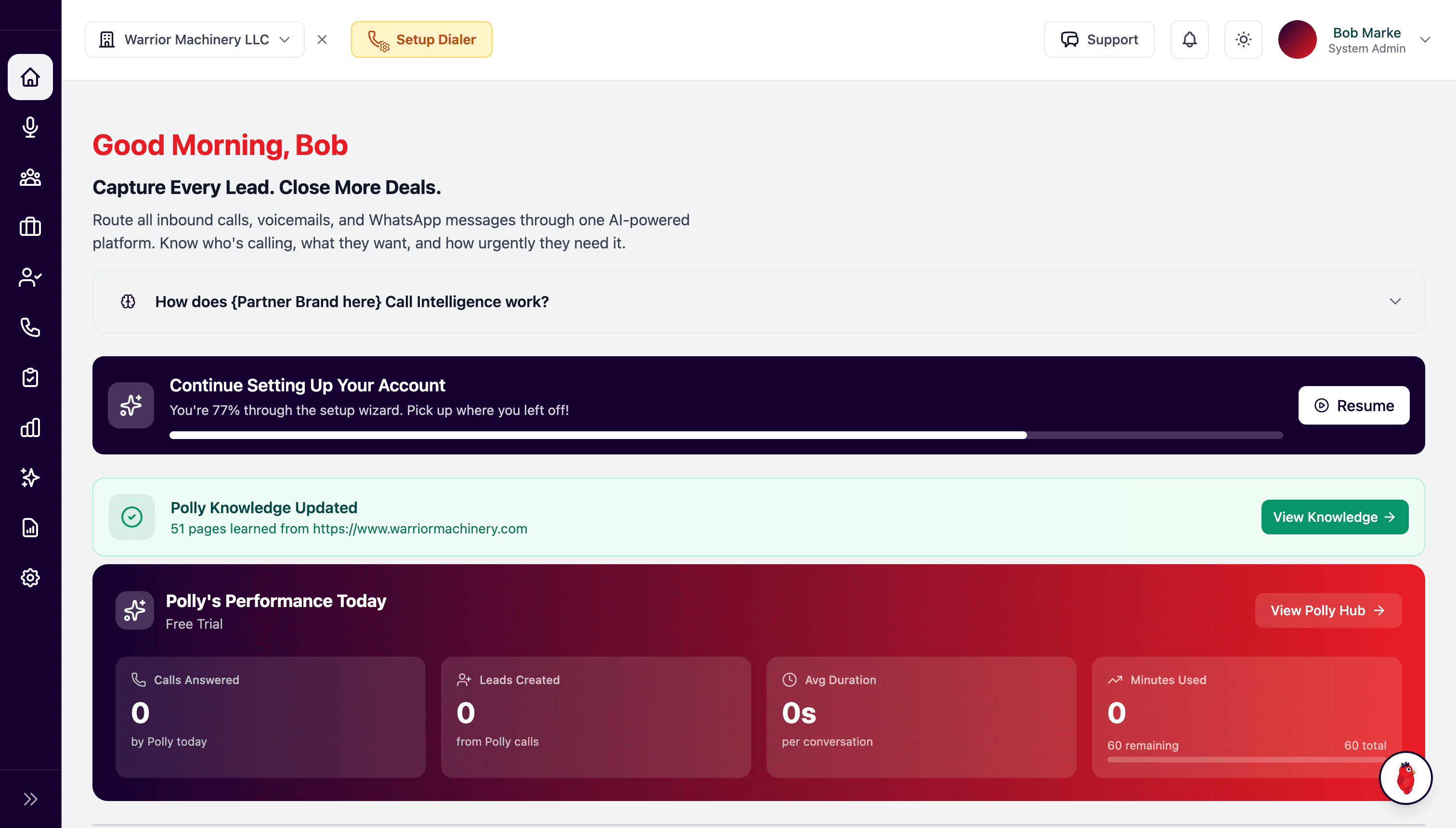
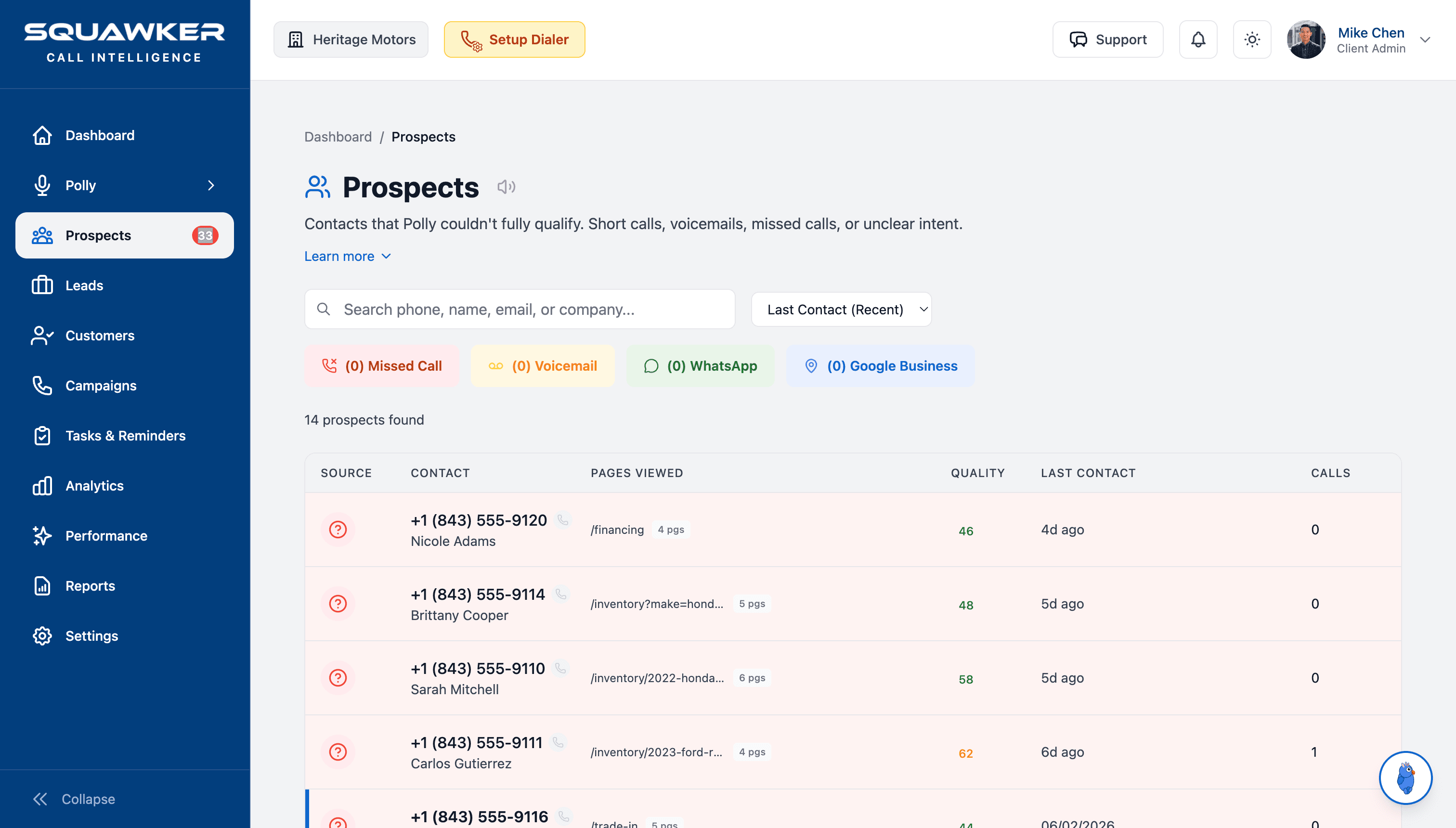
Product views
These views show how Squawker organizes conversations, records, tasks, and follow-up across the platform.
No. SOC 2 is in preparation and public copy must not imply completion.
Tenant-scoped tables use account boundaries and RLS policies so user requests only access permitted records.
The trust page should list core infrastructure and communication providers so enterprise buyers can review dependencies early.
Yes. The public page should introduce residency options, then move specific requirements into the security review conversation.
Consent requirements vary by market and deployment. Squawker should document the posture clearly and review customer-specific requirements before rollout.
Security concerns should route through the contact path with enough context for the team to triage vulnerability reports and enterprise review requests.
No. Public partner proof should stay off the trust page unless legal and commercial approval is explicit.
Procurement should review data isolation, subprocessors, retention, call consent, monitoring, incident response, and SOC 2 preparation status.
Next paths